As part of moving a Sydney University from Sun/Oracle iPlanet LDAP directory to Active Directory I have to support the educational standard objects, EduPerson, the Australian specific options required by the AFF, AuEduPerson, the university is also using the schac, the Schema for Academia. All three of these are out on the internets in different formats but not all were available for AD. I have taken these works, additional information from the schema documentation and converted them or updated them to support AD direct import. I have also be provided these to the AAF to list in there ‘files’ section of there web site.
These have all been tested on AD domain and forest modes 2003-2008r2 on Windows 2008 R2.
Make sure you turn on Advanced Features in AD users and computers to see them. And to enable the schema manager use the command “regsvr32 c:\Windows\System32\schmmgmt.dll”




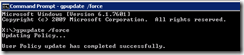
To import these files, from a Domain Controller logged on as a Schema Admin run the following, you can run this remotely to the DC, but the command line is horrible…:
ldifde -i -f "eduPerson-active directory.ldf" -v
ldifde -i -f "aueduPerson-active directory.ldf" -v
ldifde -i -f "schac-active directory.ldf" -v

You will notice in some attributes the “searchFlags: 1” setting is on for some key attributes, this is anticipating searching and managing performance, this can be changed in the GUI or in the schema once scale testing is underway, this may also need to be enabled for some POSIX / PAM settings.

Following are the three schema files.
AuEduPerson
# ========================================================================================================================
#
# File: auEduPerson-active directory.ldf
# Version: 20121130
#
# Updated by Dave Colvin, http://davestechnology.blogspot.com.au/ for direct AD import
#
# This file should be imported with the following command while logged in to the Domain Controller as an Admin User:
# ldifde -i -f -v auEduPerson.ldif
#
# REMEMBER TO SEARCH AND REPLACE DC=XXX,DC=EDU,DC=AU WITH YOUR DC SUFFIX
#
# ========================================================================================================================
# Attributes
# ========================================================================================================================
#
dn: CN=auEduPersonAffiliation,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: auEduPersonAffiliation
lDAPDisplayName: auEduPersonAffiliation
adminDisplayName: auEduPersonAffiliation
adminDescription: Specifies a person's relationship to the institution in broad categories but with a finer-grained set of permissible values than eduPersonAffiliation.
attributeID: 1.3.6.1.4.1.27856.1
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: FALSE
searchFlags: 1
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=auEduPersonLegalName,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: auEduPersonLegalName
lDAPDisplayName: auEduPersonLegalName
adminDisplayName: auEduPersonLegalName
adminDescription: The user’s legal name, as per their passport, birth certificate, or other legal document.
attributeID: 1.3.6.1.4.1.27856.2
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: TRUE
searchFlags: 1
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=auEduPersonSharedToken,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: auEduPersonSharedToken
lDAPDisplayName: auEduPersonSharedToken
adminDisplayName: auEduPersonSharedToken
adminDescription: A unique identifier enabling federation spanning services such as Grid and Repositories. Values of the identifier are generated using a set formula. The value has the following qualities: unique; opaque; non-targeted; persistent; resolvable (only by an IdP that has supplied it); not re-assignable; not mutable (refreshing the value is equivalent to creating a new identity); permitted to be displayed (Note: the value is somewhat display friendly, and may be appended to the displayName with a separating space, and used as a unique display name to be included in PKI Certificate DNs and as a resource ownership label, e.g. John Citizen ZsiAvfxa0BXULgcz7QXknbGtfxk ); and portable.
attributeID: 1.3.6.1.4.1.27856.3
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: TRUE
searchFlags: 1
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
# ========================================================================================================================
# Object classes
# ========================================================================================================================
dn: CN=auEduPerson,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: classSchema
cn: auEduPerson
lDAPDisplayName: auEduPerson
adminDisplayName: auEduPerson
adminDescription: Consists of a set of data elements or attributes about individuals within Australian higher education
governsID: 1.3.6.1.4.1.27856
objectClassCategory: 3
subclassOf: top
rdnAttId: cn
mayContain: 1.3.6.1.4.1.27856.1
mayContain: 1.3.6.1.4.1.27856.2
mayContain: 1.3.6.1.4.1.27856.3
defaultObjectCategory: CN=EduPerson,cn=Schema,cn=Configuration,DC=xxx,DC=EDU,DC=AU
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=User,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: modify
add: auxiliaryClass
auxiliaryClass: auEduPerson
-
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
# ========================================================================================================================
EduPerson
# ========================================================================================================================
#
# File: eduPerson-active directory.ldf
# Version: 200806
#
# Updated by Dave Colvin, http://davestechnology.blogspot.com.au/ for direct AD import
#
# This file should be imported with the following command while logged in to the Domain Controller as an Admin User:
# ldifde -i -f eduPerson-active directory.ldif -v
#
# REMEMBER TO SEARCH AND REPLACE DC=XXX,DC=EDU,DC=AU WITH YOUR DC SUFFIX
#
# ========================================================================================================================
# ========================================================================================================================
# Attributes
# ========================================================================================================================
dn: CN=eduPersonAffiliation,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonAffiliation
lDAPDisplayName: eduPersonAffiliation
adminDisplayName: eduPersonAffiliation
adminDescription: Specifies the person's relationship(s) to the institution, permissible values: faculty, student, staff, alum, member, affiliate, employee
attributeID: 1.3.6.1.4.1.5923.1.1.1.1
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: FALSE
searchFlags: 1
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=eduPersonNickname,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonNickname
lDAPDisplayName: eduPersonNickname
adminDisplayName: eduPersonNickname
adminDescription: Person's nickname, or the informal name by which they are accustomed to be hailed
attributeID: 1.3.6.1.4.1.5923.1.1.1.2
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: FALSE
searchFlags: 1
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=eduPersonOrgDN,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonOrgDN
lDAPDisplayName: eduPersonOrgDN
adminDisplayName: eduPersonOrgDN
adminDescription: Specifies the person's relationship(s) to the institution, permissible values: faculty, student, staff, alum, member, affiliate, employee
attributeID: 1.3.6.1.4.1.5923.1.1.1.3
attributeSyntax: 2.5.5.1
oMSyntax: 127
isSingleValued: TRUE
searchFlags: 0
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=eduPersonOrgUnitDN,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonOrgUnitDN
lDAPDisplayName: eduPersonOrgUnitDN
adminDisplayName: eduPersonOrgUnitDN
adminDescription: The distinguished name(s) (DN) of the directory entries representing the person's Organizational Unit(s)
attributeID: 1.3.6.1.4.1.5923.1.1.1.4
attributeSyntax: 2.5.5.1
oMSyntax: 127
isSingleValued: FALSE
searchFlags: 0
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=eduPersonPrimaryAffiliation,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonPrimaryAffiliation
lDAPDisplayName: eduPersonPrimaryAffiliation
adminDisplayName: eduPersonPrimaryAffiliation
adminDescription: Specifies the person's PRIMARY relationship to the institution in broad categories such as student, faculty, staff, alum, etc
attributeID: 1.3.6.1.4.1.5923.1.1.1.5
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: TRUE
searchFlags: 1
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=eduPersonPrincipalName,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonPrincipalName
lDAPDisplayName: eduPersonPrincipalName
adminDisplayName: eduPersonPrincipalName
adminDescription: The "NetID" of the person for the purposes of inter-institutional authentication. It should be represented in the form "user@scope" where scope defines a local security domain
attributeID: 1.3.6.1.4.1.5923.1.1.1.6
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: TRUE
searchFlags: 1
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=eduPersonEntitlement,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonEntitlement
lDAPDisplayName: eduPersonEntitlement
adminDisplayName: eduPersonEntitlement
adminDescription: URI (either URN or URL) that indicates a set of rights to specific resources
attributeID: 1.3.6.1.4.1.5923.1.1.1.7
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: FALSE
searchFlags: 1
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=eduPersonPrimaryOrgUnitDN,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonPrimaryOrgUnitDN
lDAPDisplayName: eduPersonPrimaryOrgUnitDN
adminDisplayName: eduPersonPrimaryOrgUnitDN
adminDescription: The distinguished name (DN) of the directory entry representing the person's primary Organizational Unit(s)
attributeID: 1.3.6.1.4.1.5923.1.1.1.8
attributeSyntax: 2.5.5.1
oMSyntax: 127
isSingleValued: TRUE
searchFlags: 0
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=eduPersonScopedAffiliation,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonScopedAffiliation
lDAPDisplayName: eduPersonScopedAffiliation
adminDisplayName: eduPersonScopedAffiliation
adminDescription: Specifies the person's affiliation (see eduPersonAffiliation) within a particular security domain, the values consist of a left (affiliation) and right component (security domain) separated by an "@" sign
attributeID: 1.3.6.1.4.1.5923.1.1.1.9
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: FALSE
searchFlags: 1
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=eduPersonTargetedID,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonTargetedID
lDAPDisplayName: eduPersonTargetedID
adminDisplayName: eduPersonTargetedID
adminDescription: Specifies the person's relationship(s) to the institution, permissible values: faculty, student, staff, alum, member, affiliate, employee
attributeID: 1.3.6.1.4.1.5923.1.1.1.10
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: FALSE
searchFlags: 0
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn: CN=eduPersonAssurance,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: eduPersonAssurance
lDAPDisplayName: eduPersonAssurance
adminDisplayName: eduPersonAssurance
adminDescription: Set of URIs that assert compliance with specific standards for identity assurance.
attributeID: 1.3.6.1.4.1.5923.1.1.1.11
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: FALSE
searchFlags: 0
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
# ========================================================================================================================
# Object classes
# ========================================================================================================================
dn: CN=eduPerson,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: classSchema
cn: eduPerson
lDAPDisplayName: eduPerson
adminDisplayName: eduPerson
adminDescription: Consists of a set of data elements or attributes about individuals within higher education
governsID: 1.3.6.1.4.1.5923.1.1.2
objectClassCategory: 3
subclassOf: top
rdnAttId: cn
mayContain: 1.3.6.1.4.1.5923.1.1.1.1
mayContain: 1.3.6.1.4.1.5923.1.1.1.2
mayContain: 1.3.6.1.4.1.5923.1.1.1.3
mayContain: 1.3.6.1.4.1.5923.1.1.1.4
mayContain: 1.3.6.1.4.1.5923.1.1.1.5
mayContain: 1.3.6.1.4.1.5923.1.1.1.6
mayContain: 1.3.6.1.4.1.5923.1.1.1.7
mayContain: 1.3.6.1.4.1.5923.1.1.1.8
mayContain: 1.3.6.1.4.1.5923.1.1.1.9
mayContain: 1.3.6.1.4.1.5923.1.1.1.10
mayContain: 1.3.6.1.4.1.5923.1.1.1.11
defaultObjectCategory: CN=eduPerson,cn=Schema,cn=Configuration,DC=xxx,DC=EDU,DC=AU
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=User,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: modify
add: auxiliaryClass
auxiliaryClass: eduPerson
-
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
# ========================================================================================================================
SchAc
# ========================================================================================================================
# Based on file Schac-Schema-1.4-Sun.ldif (non experimental schema items)
#
# File: # schac-active directory.ldf
# Version: 20121103
#
# updated by Dave Colvin, http://davestechnology.blogspot.com.au/ for AD direct import...
#
# This file should be imported with the following command while logged in to the Domain Controller as an Admin User:
# ldifde -i -f eduPerson.ldif -v
#
# REMEMBER TO SEARCH AND REPLACE DC=XXX,DC=EDU,DC=AU WITH YOUR DC SUFFIX
#
# ========================================================================================================================
# Attributes
# ========================================================================================================================
dn: cn=schacMotherTongue,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
cn: schacMotherTongue
lDAPDisplayName: schacMotherTongue
adminDisplayName: schacMotherTongue
adminDescription: RFC 3066 code for prefered language of communication
attributeID: 1.3.6.1.4.1.25178.1.2.1
attributeSyntax: 2.5.5.12
oMSyntax: 64
isSingleValued: TRUE
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacGender,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.2
attributeSyntax: 2.5.5.12
isSingleValued: TRUE
lDAPDisplayName: schacGender
cn: schacGender
oMSyntax: 64
adminDisplayName: schacGender
adminDescription: Representation of human gender (see ISO 5218)
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacDateOfBirth,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.3
attributeSyntax: 2.5.5.12
isSingleValued: TRUE
lDAPDisplayName: schacDateOfBirth
cn: schacDateOfBirth
oMSyntax: 64
adminDisplayName: schacDateOfBirth
adminDescription: Date of birth (format YYYYMMDD, only numeric chars)
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacPlaceOfBirth,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.4
attributeSyntax: 2.5.5.12
isSingleValued: TRUE
lDAPDisplayName: schacPlaceOfBirth
cn: schacPlaceOfBirth
oMSyntax: 64
adminDisplayName: schacPlaceOfBirth
adminDescription: Birth place of a person
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacCountryOfCitizenship,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.5
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacCountryOfCitizenship
cn: schacCountryOfCitizenship
oMSyntax: 64
adminDisplayName: schacCountryOfCitizenship
adminDescription: Country of citizenship of a person. Format two-letter acronym according to ISO 3166
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacSn1,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.6
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacSn1
cn: schacSn1
oMSyntax: 64
adminDisplayName: schacSn1
searchFlags: 1
showInAdvancedViewOnly: TRUE
adminDescription: First surname of a person
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacSn2,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.7
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacSn2
cn: schacSn2
oMSyntax: 64
adminDisplayName: schacSn2
searchFlags: 1
showInAdvancedViewOnly: TRUE
adminDescription: Second surname of a person
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacPersonalTitle,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.8
attributeSyntax: 2.5.5.12
isSingleValued: TRUE
lDAPDisplayName: schacPersonalTitle
cn: schacPersonalTitle
oMSyntax: 64
adminDisplayName: schacPersonalTitle
adminDescription: RFC1274: personal title
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacHomeOrganization,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.9
attributeSyntax: 2.5.5.12
isSingleValued: TRUE
lDAPDisplayName: schacHomeOrganization
cn: schacHomeOrganization
oMSyntax: 64
adminDisplayName: schacHomeOrganization
adminDescription: Domain name of the home organization
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacHomeOrganizationType,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.10
attributeSyntax: 2.5.5.12
isSingleValued: TRUE
lDAPDisplayName: schacHomeOrganizationType
cn: schacHomeOrganizationType
oMSyntax: 64
adminDisplayName: schacHomeOrganizationType
adminDescription: Type of the home organization
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacCountryOfResidence,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.11
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacCountryOfResidence
cn: schacCountryOfResidence
oMSyntax: 64
adminDisplayName: schacCountryOfResidence
adminDescription: Country of citizenship of a person. Format two-letter acronym according to ISO 3166
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacUserPresenceID,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.12
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacUserPresenceID
cn: schacUserPresenceID
oMSyntax: 64
adminDisplayName: schacUserPresenceID
adminDescription: Used to store a set of values related to the network presence
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacPersonalPosition,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.13
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacPersonalPosition
cn: schacPersonalPosition
searchFlags: 1
showInAdvancedViewOnly: TRUE
oMSyntax: 64
adminDisplayName: schacPersonalPosition
adminDescription: Position inside an institution
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacPersonalUniqueCode,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.14
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacPersonalUniqueCode
cn: schacPersonalUniqueCode
oMSyntax: 64
searchFlags: 1
showInAdvancedViewOnly: TRUE
adminDisplayName: schacPersonalUniqueCode
adminDescription: unique code for the subject
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacPersonalUniqueID,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.15
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacPersonalUniqueID
cn: schacPersonalUniqueID
oMSyntax: 64
searchFlags: 1
showInAdvancedViewOnly: TRUE
adminDisplayName: schacPersonalUniqueID
adminDescription: Unique identifier for the subject
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacExpiryDate,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.17
attributeSyntax: 2.5.5.12
isSingleValued: TRUE
lDAPDisplayName: schacExpiryDate
cn: schacExpiryDate
oMSyntax: 64
adminDisplayName: schacExpiryDate
adminDescription: Date from which the set of data is to be considered invalid (format YYYYMMDDhhmmssZ)
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacUserPrivateAttribute,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.18
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacUserPrivateAttribute
cn: schacUserPrivateAttribute
oMSyntax: 64
adminDisplayName: schacUserPrivateAttribute
adminDescription: Set of denied access attributes
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacUserStatus,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.19
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacUserStatus
cn: schacUserStatus
oMSyntax: 64
adminDisplayName: schacUserStatus
adminDescription: Used to store a set of status of a person as user of services
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacProjectMembership,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.20
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacProjectMembership
cn: schacProjectMembership
oMSyntax: 64
searchFlags: 1
showInAdvancedViewOnly: TRUE
adminDisplayName: schacProjectMembership
adminDescription: Name of the project
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacProjectSpecificRole,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.2.21
attributeSyntax: 2.5.5.12
isSingleValued: FALSE
lDAPDisplayName: schacProjectSpecificRole
cn: schacProjectSpecificRole
oMSyntax: 64
searchFlags: 1
showInAdvancedViewOnly: TRUE
adminDisplayName: schacProjectSpecificRole
adminDescription: Used to store a set of roles of a person inside a project
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: cn=schacYearOfBirth,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: top
objectClass: attributeSchema
attributeID: 1.3.6.1.4.1.25178.1.0.2.3
attributeSyntax: 2.5.5.12
isSingleValued: TRUE
lDAPDisplayName: schacYearOfBirth
cn: schacYearOfBirth
oMSyntax: 64
adminDisplayName: schacYearOfBirth
adminDescription: Year of birth (format YYYY, only numeric chars)
showInAdvancedViewOnly: TRUE
systemOnly: FALSE
dn:
changetype: Modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
# ========================================================================================================================
# Object classes
# ========================================================================================================================
dn: CN=schacPersonalCharacteristics,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: classSchema
cn: schacPersonalCharacteristics
lDAPDisplayName: schacPersonalCharacteristics
adminDisplayName: schacPersonalCharacteristics
adminDescription: Personal characteristics describe the individual person represented by the entry
governsID: 1.3.6.1.4.1.25178.1.1.1
objectClassCategory: 3
subclassOf: top
rdnAttId: cn
mayContain: 1.3.6.1.4.1.25178.1.2.8
mayContain: 1.3.6.1.4.1.25178.1.2.7
mayContain: 1.3.6.1.4.1.25178.1.2.6
mayContain: 1.3.6.1.4.1.25178.1.2.5
mayContain: 1.3.6.1.4.1.25178.1.2.4
mayContain: 1.3.6.1.4.1.25178.1.2.3
mayContain: 1.3.6.1.4.1.25178.1.2.2
mayContain: 1.3.6.1.4.1.25178.1.2.1
defaultObjectCategory: CN=schacPersonalCharacteristics,cn=Schema,cn=Configuration,DC=xxx,DC=EDU,DC=AU
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=User,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: modify
add: auxiliaryClass
auxiliaryClass: schacPersonalCharacteristics
-
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=schacContactLocation,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: classSchema
cn: schacContactLocation
lDAPDisplayName: schacContactLocation
adminDisplayName: schacContactLocation
adminDescription: Primary means of locating and contacting potential collaborators and other persons-of-interest at peer institutions
governsID: 1.3.6.1.4.1.25178.1.1.2
objectClassCategory: 3
subclassOf: top
rdnAttId: cn
mayContain: 1.3.6.1.4.1.25178.1.2.12
mayContain: 1.3.6.1.4.1.25178.1.2.11
mayContain: 1.3.6.1.4.1.25178.1.2.10
mayContain: 1.3.6.1.4.1.25178.1.2.9
defaultObjectCategory: CN=schacContactLocation,cn=Schema,cn=Configuration,DC=xxx,DC=EDU,DC=AU
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=User,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: modify
add: auxiliaryClass
auxiliaryClass: schacContactLocation
-
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=schacEmployeeInfo,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: classSchema
cn: schacEmployeeInfo
lDAPDisplayName: schacEmployeeInfo
adminDisplayName: schacEmployeeInfo
adminDescription: Employee information includes attributes that have relevance to the employee role, such as position, office hours, and job title
governsID: 1.3.6.1.4.1.25178.1.1.3
objectClassCategory: 3
subclassOf: top
rdnAttId: cn
mayContain: 1.3.6.1.4.1.25178.1.2.13
defaultObjectCategory: CN=schacEmployeeInfo,cn=Schema,cn=Configuration,DC=xxx,DC=EDU,DC=AU
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=User,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: modify
add: auxiliaryClass
auxiliaryClass: schacEmployeeInfo
-
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=schacLinkageIdentifiers,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: classSchema
cn: schacLinkageIdentifiers
lDAPDisplayName: schacLinkageIdentifiers
adminDisplayName: schacLinkageIdentifiers
adminDescription: Used to link a directory entry with records in external data stores or other directory entries
governsID: 1.3.6.1.4.1.25178
objectClassCategory: 3
subclassOf: top
rdnAttId: cn
mayContain: 1.3.6.1.4.1.25178.1.2.15
mayContain: 1.3.6.1.4.1.25178.1.2.14
defaultObjectCategory: CN=schacLinkageIdentifiers,cn=Schema,cn=Configuration,DC=xxx,DC=EDU,DC=AU
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=User,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: modify
add: auxiliaryClass
auxiliaryClass: schacLinkageIdentifiers
-
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=schacEntryMetadata,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: classSchema
cn: schacEntryMetadata
lDAPDisplayName: schacEntryMetadata
adminDisplayName: schacEntryMetadata
adminDescription: Used to contain information about the entry itself, often its status, birth, and death
governsID: 1.3.6.1.4.1.25178.1.1.5
objectClassCategory: 3
subclassOf: top
rdnAttId: cn
mayContain: 1.3.6.1.4.1.25178.1.2.17
defaultObjectCategory: CN=schacEntryMetadata,cn=Schema,cn=Configuration,DC=xxx,DC=EDU,DC=AU
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=User,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: modify
add: auxiliaryClass
auxiliaryClass: schacEntryMetadata
-
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=schacEntryConfidentiality,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: classSchema
cn: schacEntryConfidentiality
lDAPDisplayName: schacEntryConfidentiality
adminDisplayName: schacEntryConfidentiality
adminDescription: Used to indicate whether an entry is visible publicly, visible only to affiliates of the institution, or not visible at all
governsID: 1.3.6.1.4.1.25178.1.1.6
objectClassCategory: 3
subclassOf: top
rdnAttId: cn
mayContain: 1.3.6.1.4.1.25178.1.2.18
defaultObjectCategory: CN=schacEntryConfidentiality,cn=Schema,cn=Configuration,DC=xxx,DC=EDU,DC=AU
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=User,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: modify
add: auxiliaryClass
auxiliaryClass: schacEntryConfidentiality
-
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=schacUserEntitlements,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: classSchema
cn: schacUserEntitlements
lDAPDisplayName: schacUserEntitlements
adminDisplayName: schacUserEntitlements
adminDescription: Authorization for services
governsID: 1.3.6.1.4.1.25178.1.1.7
objectClassCategory: 3
subclassOf: top
rdnAttId: cn
mayContain: 1.3.6.1.4.1.25178.1.2.19
defaultObjectCategory: CN=schacUserEntitlements,cn=Schema,cn=Configuration,DC=xxx,DC=EDU,DC=AU
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=User,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: modify
add: auxiliaryClass
auxiliaryClass: schacUserEntitlements
-
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=schacGroupMembership,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: ntdsschemaadd
objectClass: classSchema
cn: schacGroupMembership
lDAPDisplayName: schacGroupMembership
adminDisplayName: schacGroupMembership
adminDescription: Groups used to provide/restrict authorization to entries and attributes
governsID: 1.3.6.1.4.1.25178.1.1.8
objectClassCategory: 3
subclassOf: top
rdnAttId: cn
mayContain: 1.3.6.1.4.1.25178.1.2.21
mayContain: 1.3.6.1.4.1.25178.1.2.20
defaultObjectCategory: CN=schacGroupMembership,cn=Schema,cn=Configuration,DC=xxx,DC=EDU,DC=AU
systemOnly: FALSE
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
dn: CN=User,CN=Schema,CN=Configuration,DC=xxx,DC=EDU,DC=AU
changetype: modify
add: auxiliaryClass
auxiliaryClass: schacGroupMembership
-
dn:
changetype: modify
add: schemaUpdateNow
schemaUpdateNow: 1
-
# ========================================================================================================================